In a digitalized world full of computers, IoT devices and networked industrial systems, it is crucial that technology function reliably and that attackers cannot manipulate systems or data. Security doesn’t begin at the application level, but rather starts right in the hardware and software. Fraunhofer AISEC cybersecurity researcher Dr. Michael Weiss and his team are researching solutions implementing security mechanisms in chips. In the interview with the FMD, he explains how components are made to be protected and trustworthy. He provides insight in the concept of secure containers and explains the role played by open standards such as RISC-V.
Mr. Weiss, you have been working in the Secure Operating Systems department at Fraunhofer AISEC since 2010. Can you briefly outline what you do?
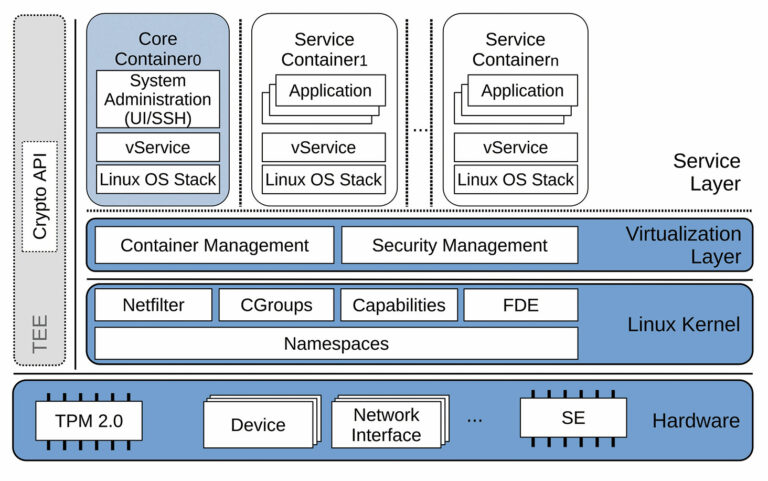
In our department, we work on the interface between hardware and software. Our primary concern is ensuring that software runs securely on systems such as microcontrollers or on larger operating systems such as Linux or Windows. So, in principle, we ensure that storage areas are protected, that different applications run isolated from each other and that virtualization can be used to provide trusted environments. This enables us to ensure that software components run securely even if attackers attempt to manipulate the system.
One topic with a major role in your work is GyroidOS. What exactly is that?
GyroidOS is a virtualization platform on the operating system level that was developed at Fraunhofer AISEC. Its focus is on security, especially in running isolated applications.
The principle can be explained with the terms virtualization and containers. Virtualization means that multiple separate virtual environments can run on a single physical system, acting as independent systems. Applications run isolated in these environments, the containers. They only access those resources that are assigned to them and cannot influence the rest of the system. Also, data is often stored in encrypted form for additional protection. GyroidOS specifically uses this concept. Each container is isolated and ensures a clearly defined level of security, allowing different applications to run in parallel on the same computer without compromising each other.
Does GyroidOS require special hardware for this?
GyroidOS essentially works without hardware support. It uses Linux kernel mechanisms such as memory isolation and encryption to securely operate containers. For especially high security requirements GyroidOS can also use trusted hardware anchors such as chips from the OpenTitan project or Trusted Platform Module (TPM) chips. This hardware ensures checking of the system startup process and the integrity of key components. GyroidOS then builds on this foundation. The containers are isolated, and additional security mechanisms such as hard disk encryption or software component signing establish a chain of trust from the hardware anchor to the application level. GyroidOS combines software isolation with hardware-based protection. This is especially effective in security-critical applications.
Which applications run in GyroidOS containers?
GyroidOS is highly flexible and is independent of any specific application. A good example is a mobile ad hoc network for emergency services. Basic communication runs in an open container, while sensitive communication, such as via a VPN, runs in an isolated, secure container. This protects data and prevents them from being unintentionally passed on to others.
GyroidOS is also implemented in telecommunications and 6G, such as in the 6G ANNA project. This system uses containers to run critical communication processes in an isolated environment, while other applications run in parallel on the same hardware without causing security risks.
How long has GyroidOS been in development?
The idea originally came to life as part of a scientific publication in 2012 as a concept for secure environments on mobile devices. The platform was adapted for IoT applications in 2018, especially for trusted connector scenarios. GyroidOS is now a mature platform and is already being used in industrial projects, both in the IoT sector and in cloud contexts.
What makes your institute's work in this area stand out?
At Fraunhofer AISEC, we combine hardware and software expertise to implement comprehensive security mechanisms. We working with open standards such as RISC-V and OpenTitan to establish trust in chips and we are transferring these security concepts to complex applications. This sets us apart because many other approaches account for only hardware or only software. In contrast, our approach focuses on the entire chain of trust from the chip to the application. This makes modern networked systems significantly more secure.
We have already briefly discussed OpenTitan, but what does RISC-V have to do with GyroidOS?
RISC-V is an open hardware architecture on which secure platforms such as GyroidOS can run. It is freely accessible, similar to open-source software. This means that anyone can design their own chips or expand existing designs based on the specification.
At Fraunhofer AISEC, GyroidOS is used in a secure system-on-chip (SSoC) context. We are developing a hardware platform that is based in part on OpenTitan chips and runs on a RISC-V processor. Our colleagues in the Hardware Security Department work together with those in Fraunhofer IIS to design the chips, while we in the Operating System Security Department focus on the interfaces and secure execution of the software. This yields a combined software/hardware design implementing security mechanisms on both the hardware and operating system levels.
Chip development is tested and implemented in multiple steps to ensure that the concepts from the combined software/hardware work on real hardware. An emulator prototype is first used. This enables virtual testing of the hardware architecture before a physical chip even exists. The emulator runs the same software stacks that would later be executed on the real hardware. The design is then tested on a field-programmable gate array (FPGA), which is a programmable hardware component, before final chip production is started.
Containers can be operated on all of these virtual machines. GyroidOS ensures that containers remain isolated even in a cloud environment. This enables the execution of encrypted, secure workloads that are especially relevant for businesses and critical applications. The same hardware and software chain of trust that we use in the embedded sector can also be implemented in the cloud.

Emulator prototype
An emulator prototype is a virtual replica of a hardware platform allowing software to be tested before the actual hardware exists. An emulator simulates the behavior of the future chip or system on a normal computer. Developers can run, test and optimize operating systems, drivers or security mechanisms on this virtual platform. This enables early detection of errors and security vulnerabilities without the need to wait for the physical hardware. After successful testing, the software is then transferred to an FPGA or to the finished hardware.
What are the biggest challenges that your work poses?
One of the biggest challenges is to combine all the security mechanisms in a meaningful way. Each mechanism increases security, but can also reduce performance or affect usability. For example, authentication keys have to be managed and PINs or tokens have to be used—this can be difficult in an IoT device that runs autonomously. So we have to find solutions that are both secure and practical.
Let's take a look into the future. How will GyroidOS be further developed?
GyroidOS is not a finished software product; it is a platform that is undergoing continuous development. New features result from further developments in the Linux kernel, from hardware mechanisms or from research topics such as quantum cryptography. The goal is to ensure that all mechanisms—from secure boot and hardware support to confidential computing—can be used in different use cases.
Verifiability is especially important: Users should be able to verify that the software is running in a secure environment. This goes beyond simple certificates. All executed code snippets have to be measurable, so it is possible to trace which software is actually running on a trusted platform.
What is the long-term significance of the work in your Secure Operating Systems department for the protection of critical infrastructures and our digital sovereignty?
Our work ensures reliable, trustworthy and secure operation of digital systems—from smartphones and networked industrial systems to critical infrastructures such as energy supply and telecommunications. If hardware and software do not work together correctly or attackers gain uncontrolled access, data can be stolen, processes manipulated or entire systems paralyzed.
With GyroidOS and its underlying security mechanisms, we create chains of trust that ensure that every software component is verifiable and protected. Not only does this protect companies from cyberattacks, it also protects all of us, because it makes our data, communications and devices more secure. At the same time, work on open standards like RISC-V helps make the technology usable by industry and research worldwide.
This interview was originally published by Fraunhofer Group for Microelectronics in cooperation with the Leibniz institutes IHP and FBH (FMD). You can find it in German here: Secure System-on-Chip: GyroidOS, RISC-V und Hardware-Sicherheit | Interviews | FMD.insight

Dr. Michael Weiß
Michael Weiß is a cybersecurity researcher in the Secure Operating Systems department at Fraunhofer AISEC. He studied computer science at the Technical University of Munich, completing his master’s thesis at Fraunhofer AISEC on relay attacks against RFID-based ID and payment systems and his PhD on microkernel-based secure architectures and side-channel attacks in virtualized embedded devices. Since 2010, he has been working at Fraunhofer AISEC, where he leads research and industry projects on secure operating systems, virtualization and trusted execution, and is one of the main architects of the GyroidOS secure virtualization platform.
Contact: michael.weiss@aisec.fraunhofer.de